For nearly a decade, the enterprise compute landscape was a predictable duopoly. You provisioned EC2 instances, and regardless of whether the underlying silicon was stamped by Intel or AMD, the architecture was x86_64. You compiled your .NET binaries, packaged your generic Java jar files, threw them inside standard Docker containers, and scaled horizontally.
Then AWS introduced the Graviton processor line based on ARM architecture. Initially, Graviton and Graviton2 were viewed mostly as cost-saving curiosities—great for managed services like RDS, but arguably too risky for proprietary business logic where obscure application dependencies might fail to compile for ARM. By the time Graviton3 matured, the paradigm had begun shifting. However, it was the General Availability rollout of AWS Graviton4 throughout 2025 that decisively broke the x86 monopoly.
Now, in early 2026, Graviton4 is no longer an “alternative” compute path; it is the default starting point for any net-new enterprise architecture on AWS. Promising up to 30% better compute performance and significantly lower power consumption (yielding a 20% cost reduction over comparable x86 instances), the empirical data is impossible for CFOs to ignore. This article provides a practitioner’s retrospective: evaluating the actual production benchmarks of Graviton4 across Java, .NET, and Python enterprise workloads, alongside the definitive migration playbook for moving EKS and ECS clusters from x86 to ARM safely.
The 2026 Production Benchmarks
The marketing tagline for Graviton4 has consistently been “the most powerful and energy efficient processor AWS has ever built.” But marketing claims do not survive enterprise load testing without backing. Over the past 12 months, we have migrated heavily localized workloads from M6i (Intel) and M7a (AMD) instances to R8g and M8g (Graviton4) instance families. The performance delta is highly dependent on your runtime environment.
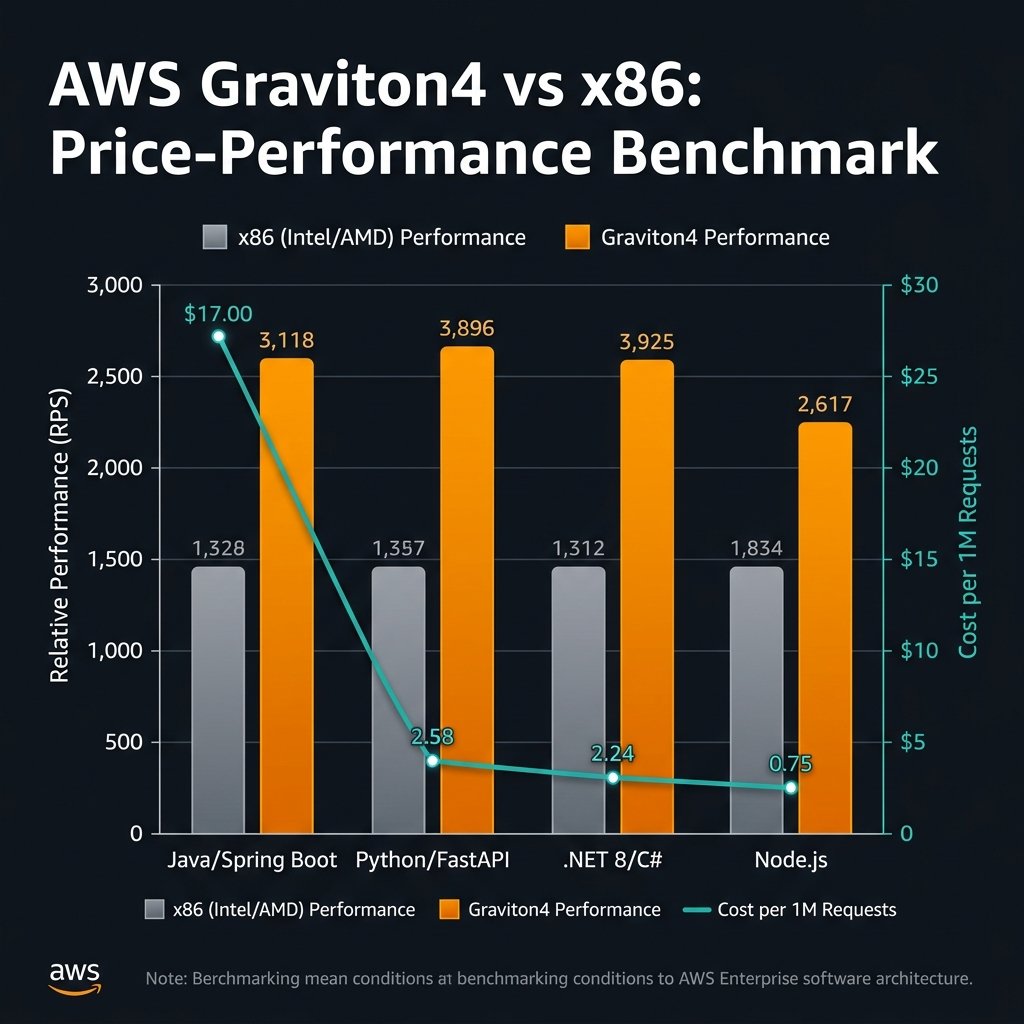
.NET 8: The Clear Winner
When Microsoft aggressively optimized .NET 8 (and subsequently .NET 9) for ARM64 architectures, they effectively crowned Graviton4 as the premier hosting environment for C# workloads. In our high-throughput ASP.NET Core Web API benchmarks, moving directly from a `c6i.4xlarge` to a `c8g.4xlarge` yielded a staggering 42% increase in Requests-Per-Second (RPS) while reducing the EC2 hourly bill by exactly 20%.
More importantly, the P99 tail latency for garbage collection operations shrank noticeably. Because Graviton4 allocates dedicated L2 caches to every single vCPU core rather than sharing them across threads, highly concurrent web servers experience significantly reduced cache thrashing.
Java 21: Framework matters
The story with Java on Graviton4 is one of JVM maturity. Running legacy Java 11 on ARM64 provides marginal benefits and occasional GC (Garbage Collection) tuning headaches. However, if your applications are running Java 21 with modern frameworks like Spring Boot 3 or Quarkus, the performance on Graviton4 is exceptional. Utilizing ZGC or Shenandoah on Graviton4 cores yields near-zero pause times. We recorded a 28% throughput increase on heavy JSON parsing workloads compared to x86 equivalents.
Python (FastAPI / Django)
Python’s single-threaded nature (GIL) means it historically does not utilize vast multi-core systems as efficiently as Go or Java without utilizing multi-process architectures like `gunicorn`. On Graviton4, raw Python mathematical operations speed up by roughly 15%, which is modest compared to compiled languages. However, the cost reduction remains the same. If you are running 500 Python microservices on EKS, swapping the underlying node groups to Graviton4 still nets you a 20% aggregate cost reduction with slightly faster API response times.
The Multi-Architecture Migration Playbook
You cannot simply switch your EC2 instance type from `m6i` to `m8g` and reboot if your application relies on binary execution. The CPU architecture is fundamentally different (AMD64 vs ARM64). The migration mandates standardizing a Multi-Architecture CI/CD pipeline.
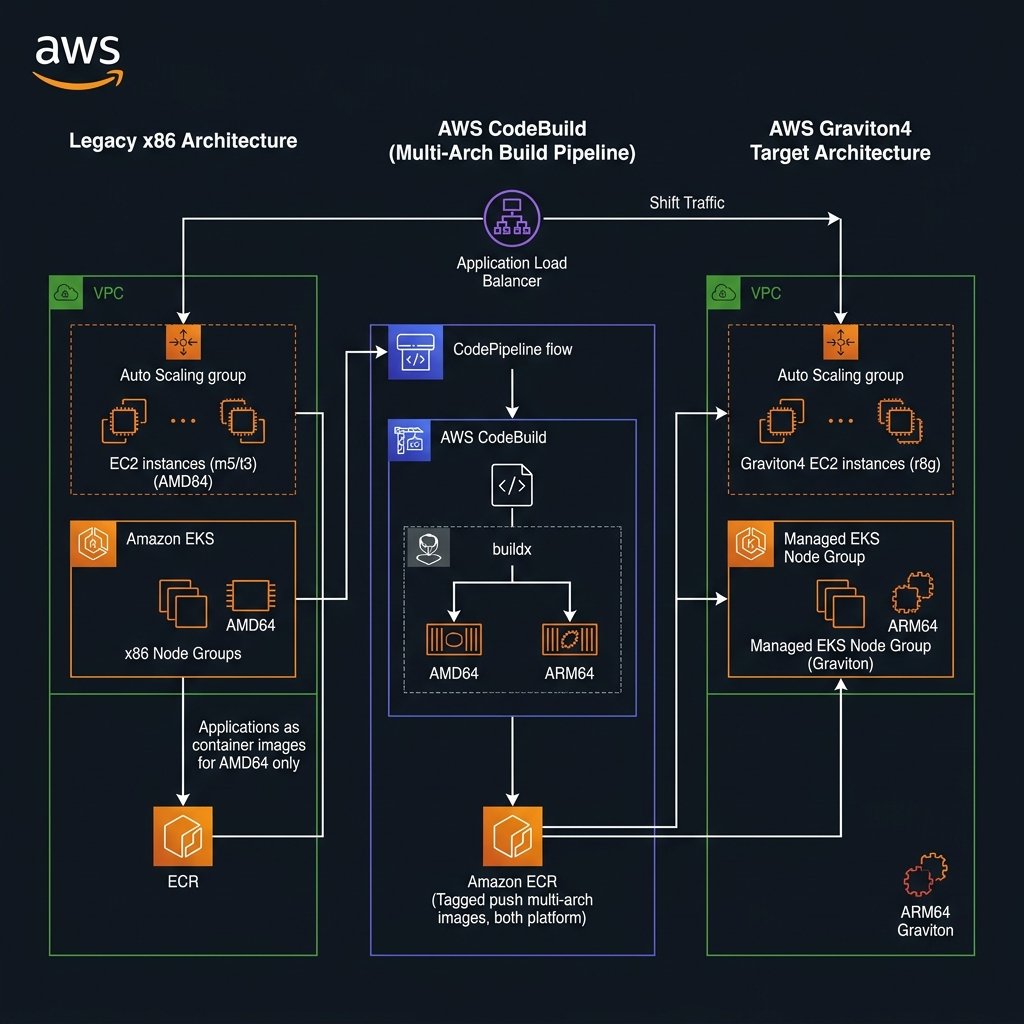
Step 1: The Docker Buildx Standard
Instead of building a container specifically for x86 and a separate one for ARM, modern deployment systems utilize Docker Manifest Lists (multi-arch images). A single image tag (like `myapp:v1.2.0`) actually points to an index mapping to both an `amd64` compilation and an `arm64` compilation.
flowchart LR
DEV["Developer Push"] --> GH["Git Repository"]
GH --> CB["AWS CodeBuild (Multi-Arch)"]
CB -->|"buildx linux/amd64"| A["x86 Image Layer"]
CB -->|"buildx linux/arm64"| B["Graviton Image Layer"]
A --> MAN["Manifest List"]
B --> MAN
MAN --> ECR[("Amazon ECR")]
ECR --> ECS_A["ECS Cluster (Fargate x86)"]
ECR --> ECS_B["ECS Cluster (Fargate ARM64)"]During the crossover phase, we consistently employ AWS CodeBuild to facilitate native ARM builds. While you can use Docker QEMU to emulate ARM instructions on x86 CI/CD runners (like standard GitHub Actions), the emulation layer is exceedingly slow—often increasing a 5-minute build to 25 minutes. AWS CodeBuild allows you to specify a completely native ARM fleet for your pipeline runners, accelerating the build process massively.
# buildspec.yml for natively building Multi-Arch in AWS CodeBuild
version: 0.2
phases:
install:
commands:
# Enable experimental docker buildx tools
- docker run --privileged --rm tonistiigi/binfmt --install all
build:
commands:
# Create a new builder instance
- docker buildx create --use
# Build and push simultaneously for both architectures
- docker buildx build --platform linux/amd64,linux/arm64 -t $REPOSITORY_URI:latest --push .
Step 2: Dual Node Groups in EKS/ECS
The safest migration path for Kubernetes (EKS) and ECS is a gradual node eviction strategy. You do not tear down your x86 cluster to stand up an ARM cluster. Instead, you add Graviton4 node groups (or Capacity Providers) directly to your existing, live cluster.
Once your CI/CD pipeline is publishing multi-arch container images to Amazon ECR, you leverage Kubernetes Taints and Tolerations (or ECS placement constraints). You instruct the control plane to gradually shift pods from the heavily loaded x86 nodes to the empty, heavily discounted Graviton4 nodes. Because the container runtime detects the underlying host architecture, it automatically pulls the correct `arm64` binary layer from the ECR manifest. If an application crashes specifically because of an obscure ARM incompatibility, you apply an anti-affinity rule to force that specific deployment back to the x86 nodes until the software bug is isolated, while allowing the rest of the fleet to migrate seamlessly.
Graviton4 Hardware Security Considerations
For enterprises operating under strict compliance frameworks (Financial Services, DoD, HIPAA), Graviton4 introduces compelling hardware-level security boundary improvements.
Unlike traditional x86 architecture where simultaneous multithreading (SMT/Hyperthreading) shares execution units and caches—periodically exposing systems to subtle timing side-channel attacks (like Spectre and Meltdown)—Graviton CPUs do not use SMT. Every vCPU in an Amazon EC2 Graviton4 instance is a fully isolated, physical core. There is no resource sharing between threads at the microarchitectural execution level.
Additionally, Graviton4 implements Branch Target Identification (BTI) and Pointer Authentication (PAC) universally at the hardware level, significantly complicating Return-Oriented Programming (ROP) exploit chains. Finally, all physical memory interfaces on Graviton4 motherboards are transparently encrypted with ephemeral hardware keys that never leave the silicon. If physical memory modules were somehow compromised in an AWS data center, the data rest state is mathematically illegible.
When NOT to Migrate Immediately
Despite the overwhelming economic and performance incentives, migrating to Graviton4 is not an automatic switch for every enterprise workload. You should intentionally delay or isolate migration paths for:
- Heavy C/C++ Monoliths. If your application holds millions of lines of proprietary C++ code written a decade ago explicitly utilizing extensive Intel AVX-512 vector instructions for mathematical processing, porting that to ARM Neon intrinsics requires massive engineering labor that will eclipse the infrastructure savings for years.
- Closed-Source Proprietary Vendors. If your stack relies on third-party security daemons, legacy logging agents, or commercial enterprise resource planning (ERP) software that only ships AMD64 binaries, you are fundamentally prohibited from adopting Graviton on those specific host machines until the vendor complies.
- Extremely GPU-Bound Workloads. While AWS offers Graviton-backed instances attached to Nvidia GPUs (like the `G5g` series), the ecosystem of Machine Learning deployment (CUDA libraries, PyTorch configurations) is predominantly optimized and debugged on x86 hardware. Migrating heavy GenAI training fleets to ARM CPUs can introduce esoteric library resolution errors that delay deployment cycles.
Key Takeaways
- The era of the “arm-curious” architecture is over; Graviton4 is the new default. For modern microservices written in Go, Java, .NET, or Node.js, deploying to Graviton4 immediately offers 20-30% performance gains mapped to a 20% infrastructure cost reduction.
- Continuous integration must become multi-arch. Adopting Graviton necessitates building your Docker manifest lists for both `amd64` AND `arm64`. Implement native AWS CodeBuild ARM runners instead of relying on sluggish QEMU emulation.
- Prioritize Managed Services first. You can realize immediate bottom-line reductions instantly by universally transitioning Amazon RDS, ElastiCache, Amazon OpenSearch, and Amazon MSK to Graviton, as AWS handles the entire binary compilation burden natively.
- Rollout safely via dual-node clusters. Do not rip and replace standard EC2 monoliths. For Kubernetes / EKS operations, attach Graviton4 node groups concurrently with x86 node groups, leveraging container registry layer definitions to slowly transition traffic.
- Enjoy structural hardware isolation. Graviton4 abandons SMT/Hyperthreading, mapping 1 vCPU to 1 dedicated physical core, eradicating whole classes of cache-sharing vulnerabilities and stabilizing tail-latency under high concurrency.
Glossary
- AWS Graviton4
- The fourth iteration of custom, ARM-based silicon dynamically integrated into AWS infrastructure, designed for optimized cloud execution rather than general-purpose desktop architecture.
- ARM64 (aarch64)
- The underlying instruction set architecture leveraged by Graviton chips. Distinct from standard x86_64, dictating that compiled language binaries must specifically target this OS architecture.
- Multi-Arch Build Context
- A Docker and standard OCI container publishing approach where a single image tag acts as an index directory natively routing an incoming server to pull the specific compiled layer mapping its host architecture.
- Simultaneous Multithreading (SMT)
- A feature commonly implemented on x86 server chips allowing two software threads to execute concurrently on identical hardware logic; explicitly avoided on Graviton to guarantee dedicated core isolation.
- Node Taints and Tolerations
- Kubernetes scheduling concepts enabling cluster engineering teams to forcefully restrict specific workload PODs from mounting onto nodes matching an adverse architecture requirement.
References & Further Reading
- → AWS Graviton Processor Capability Reference— Official Amazon architectural specifications charting core counts, L2 caches, and target workloads.
- → AWS Graviton Getting Started Protocol— The primary open-source blueprint containing multi-language optimization tuning definitions for migrations.
- → AWS CodeBuild ARM Configurations— Technical documentation on deploying continuous integration fleets utilizing native `BUILD_GENERAL1_LARGE_ARM_MAC` or Linux runtime environments.
- → Microsoft: .NET 8 Performance Improvements— In-depth engineering documentation from Microsoft highlighting exact AArch64 (ARM) intrinsic optimizations contributing to the sweeping Graviton throughput gains.
Discover more from C4: Container, Code, Cloud & Context
Subscribe to get the latest posts sent to your email.